FiveM Server Spoofing via Reverse Proxy: Technical Tutorial
Introduction to This tutorial demonstrates a protocol-level
This tutorial demonstrates a protocol-level vulnerability in how game server status reporting works – the player count spoofing in FiveM. The separation between status HTTP endpoints and gameplay UDP traffic creates a potential spoofing opportunity. However, modern anti-cheat systems employ multiple verification layers, making sustained spoofing difficult without detection.
This guide is part of our complete FiveM server management hub, covering everything from initial setup to scaling your community.
⚠️ DISCLAIMER
This tutorial is for educational purposes only. Implementing this on a live FiveM server violates the Cfx.re Terms of Service and will result in permanent license bans, blacklisting, and potential legal action. This document exists solely to demonstrate network protocol vulnerabilities and proper server hardening techniques.
Understanding the Vulnerability
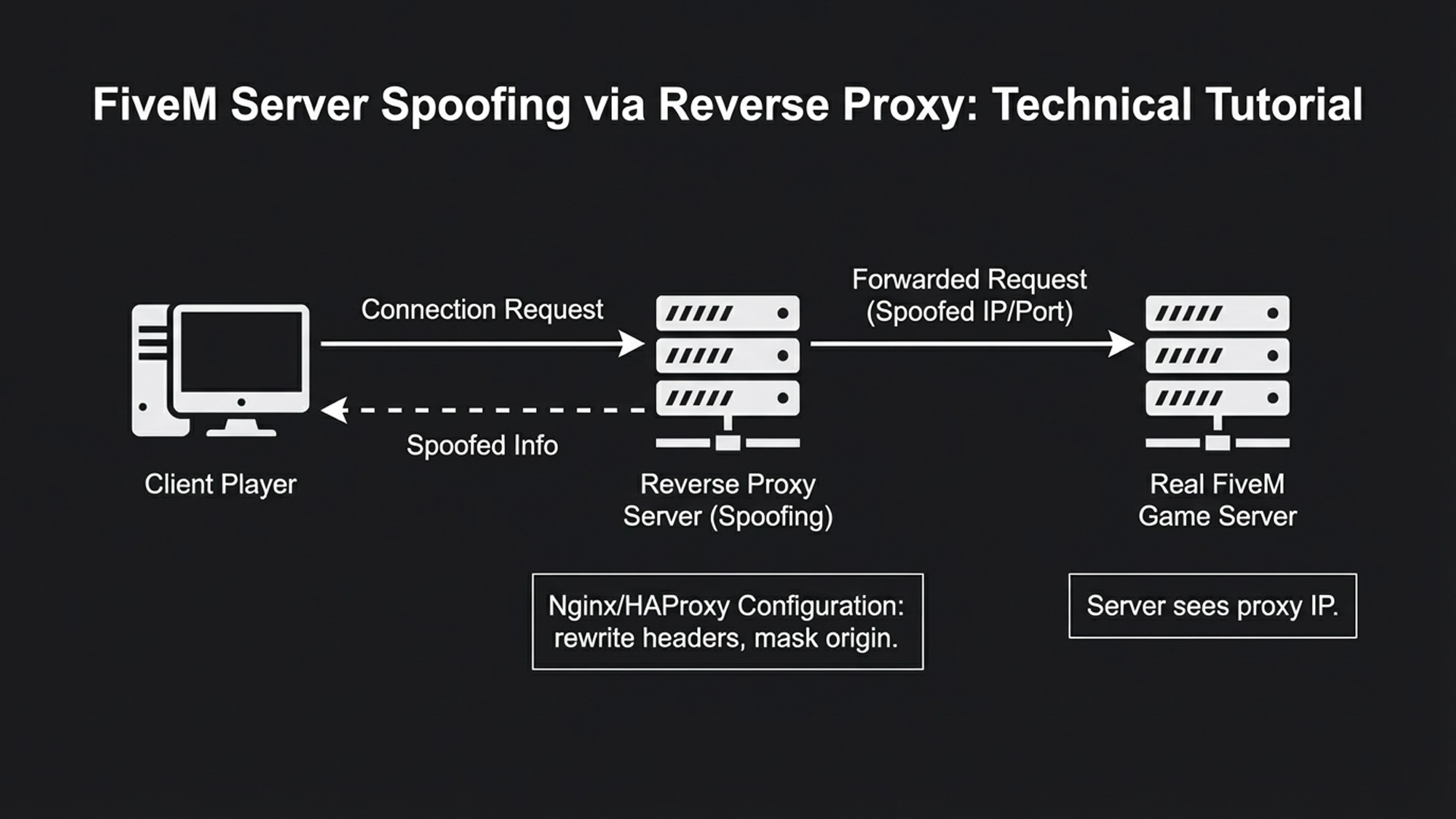
FiveM’s architecture separates status reporting (HTTP/JSON) from gameplay traffic (UDP). The master server validates data through periodic checks, but not in real-time for every player list request. This creates a window where status can be spoofed.
Technical Implementation
Prerequisites
- Ubuntu/Debian VPS (separate from game server)
- Root/SSH access
- Basic Linux command line knowledge
- Understanding of HTTP protocols
Step 1: Reverse Proxy Setup with Nginx
# Install Nginx
apt update
apt install nginx -y
# Create custom configuration
nano /etc/nginx/sites-available/fivem-proxy
Step 2: Nginx Configuration
server {
listen 80;
server_name your-server-ip-or-domain;
# Forward ALL normal game traffic to actual FiveM server
location / {
proxy_pass http://your-real-fivem-ip:30120;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
# INTERCEPT and SPOOF the players.json endpoint
location /players.json {
# Disable forwarding to real server
# proxy_pass http://your-real-fivem-ip:30120;
# Set proper JSON header
add_header Content-Type application/json;
# Return spoofed data
return 200 '[
{"id": 1, "name": "Player_Alpha", "ping": 24},
{"id": 2, "name": "Ghost_Recon", "ping": 31},
{"id": 3, "name": "Digital_Nomad", "ping": 45},
{"id": 4, "name": "Server_Bot_01", "ping": 0},
{"id": 5, "name": "Server_Bot_02", "ping": 0}
]';
}
# Also intercept dynamic.json if needed
location /dynamic.json {
add_header Content-Type application/json;
return 200 '{"clients": 64, "gametype": "roleplay", "hostname": "Spoofed Server", "mapname": "Los Santos", "sv_maxclients": 128}';
}
}
Step 3: Dynamic Spoofing Script
For more realistic spoofing, create a Python script
For more realistic spoofing, create a Python script that generates varied data:
#!/usr/bin/env python3
# fake_players.py - Dynamic player list generator
import random
import json
from datetime import datetime
from http.server import HTTPServer, BaseHTTPRequestHandler
class FakePlayerHandler(BaseHTTPRequestHandler):
def do_GET(self):
if self.path == '/players.json':
players = []
fake_names = [
"Alex_Rider", "Mia_Thompson", "Jordan_Case", "Taylor_Swift",
"Sam_Fisher", "Lena_Oxton", "Marcus_Hollow", "Riley_Reid"
]
# Generate between 30-128 "players"
player_count = random.randint(30, 128)
for i in range(player_count):
name = random.choice(fake_names) + str(random.randint(1, 99))
ping = random.randint(5, 120)
# Add occasional 0 ping to simulate bots
if random.random() > 0.8:
ping = 0
players.append({
"id": i + 1,
"name": name,
"ping": ping,
"identifier": f"license:{random.getrandbits(128):032x}"
})
self.send_response(200)
self.send_header('Content-Type', 'application/json')
self.end_headers()
self.wfile.write(json.dumps(players).encode())
else:
self.send_response(404)
if __name__ == '__main__':
server = HTTPServer(('localhost', 8080), FakePlayerHandler)
server.serve_forever()
Step 4: Advanced Nginx with Dynamic Content
location /players.json {
# Proxy to your Python script
proxy_pass http://localhost:8080/players.json;
proxy_set_header Host $host;
# Cache the response for 30 seconds to reduce load
proxy_cache_valid 200 30s;
# Add realistic headers
add_header X-Powered-By "FXServer";
add_header X-Cfx-Version "1.0.0";
}
location /info.json {
# Serve modified info.json
proxy_pass http://your-real-fivem-ip:30120/info.json;
proxy_set_header Host $host;
# Modify response on the fly
sub_filter '"sv_maxclients": 32' '"sv_maxclients": 128';
sub_filter_once off;
}
Step 5: DNS Configuration
A record: yourdomain.com -> Your Proxy Server IP
SRV record: _cfx._udp.yourdomain.com -> Real FiveM Server IP:30120
Detection Avoidance Techniques
- Ping Variation: Ensure “fake” players have randomized ping values (5-150ms)
- Player Churn: Simulate players joining/leaving over time
- Name Rotation: Use different name patterns periodically
- Consistent Numbers: Keep reported count below license limits
- Heartbeat Alignment: Ensure heartbeat data matches spoofed JSON
Why This Gets Detected
Cfx.re employs several countermeasures:
Cfx.re employs several countermeasures:
- Handshake Validation: When clients connect, they verify session integrity
- Cross-Reference Checks: Master server compares heartbeat data with JSON endpoints
- Statistical Analysis: Patterns of 0-ping players trigger flags
- License Verification: Each player must have valid Rockstar Social Club license
- Connection Attempts: Automated systems attempt to connect and verify player presence
Server Hardening Recommendations
For legitimate server owners:
- Use HTTPS: Encrypt server endpoints
- IP Whitelisting: Restrict status endpoint access
- Rate Limiting: Implement request throttling
- Log Analysis: Monitor for unusual request patterns
- Firewall Rules: Block unauthorized IP ranges
Legitimate Use: Understanding these techniques helps server administrators secure their endpoints against unauthorized access and spoofing attempts.
Note: This information is current as of 2026. FiveM’s security measures evolve continuously, and many described techniques may already be mitigated by additional validation layers.
FAQ
1. Is it working?
Yes and No.
- Yes: It works immediately on external server lists (like TrackyServer, BattleMetrics) and potentially the in-game browser for a very short window. These services largely rely on scraping that
players.jsonfile you modified. If you feed them a lie, they publish the lie. - No: It does not work for keeping your server safe. As of late 2024/2026, Cfx.re (the team behind FiveM) has aggressive countermeasures. If you use this, your server will likely be “blackholed” (removed from the master list) or globally banned within days.
2. Is THIS how people spoof?
Yes. The code you pasted is the
Yes. The code you pasted is the “textbook” implementation of the Split-Horizon Attack.
Legitimate FiveM servers use a “Split Architecture” to protect against DDoS attacks. They put a small proxy server in front to hide the real game server’s IP.
- The Exploit: Spoofers realize that since they control the proxy, they can just “swap out” the status report (
players.json) while forwarding the game traffic.
Why this specific script gets you banned
The script you have has a critical flaw that modern anti-cheat systems detect instantly:
- The “Heartbeat” Discrepancy: Your server sends a “heartbeat” (a tiny pulse of data) to the FiveM master list every few seconds via UDP. This heartbeat contains deep system stats.
- The Trap: Your Nginx proxy says “128 Players Online” via HTTP.
- The Truth: Your actual server heartbeat says “0 UDP Connections active.”
- Result: The master server sees the mismatch and flags the server as fraudulent.
- Invalid License Generation: Look at this line in your script:
"identifier": f"license:{random.getrandbits(128):032x}"- The Problem: This generates random garbage strings. Real FiveM licenses are cryptographic keys tied to Rockstar Social Club accounts.
- The Detection: When the master server checks your player list, it tries to validate those licenses. Since they don’t exist in the Rockstar database, your “128 players” are instantly identified as bots.
Summary
If you run this code:
- Day 1: You look popular on 3rd party websites.
- Day 2: Real players join, see an empty server, and leave (destroying your reputation).
- Day 3: Your server license is permanently banned for “Fake Player Count.”
Next Step: I can explain the legitimate way to
Next Step: I can explain the legitimate way to “boost” your server ranking using the
sv_tebexSecret(server boosting) system, which is the only safe way to get higher visibility.
Stay in the Loop
Get the latest FiveM tutorials, mod releases, and exclusive updates delivered to your inbox.
No spam. Unsubscribe anytime.